In the Cloud or on-Premises? Self Assessment or ISO 27001, PCI-DSS, GDPR, HIPPA, FERPA, etc? Cetbix® ISMS will boost your certification. Paperless information security management system. A better choice for organizations looking for ISMS that relates to data security. In the cybersecurity zone, the Cetbix® standards for best practice have been developed to provide guidance to organizations wishing to defend their data and business assets from cybercrimes. These standards cover, in addition to other things, the prerequisites for data security, business progression, and risk analysis.
Unlock Faster, Smarter Decisions: Sharpen Your Risk Visibility Today!
![]() Standardized risk management framework with uniform assessment methodologies enables streamlined processes for risk identification, assessment, monitoring, and mitigation. Improved risk visibility allows for smarter decision-making and a more secure and resilient future.
Standardized risk management framework with uniform assessment methodologies enables streamlined processes for risk identification, assessment, monitoring, and mitigation. Improved risk visibility allows for smarter decision-making and a more secure and resilient future.![]() Provide timely risk intelligence through reports, dashboards, and advanced analytics to promote agility, informed decision-making, and loss reduction.
Provide timely risk intelligence through reports, dashboards, and advanced analytics to promote agility, informed decision-making, and loss reduction.![]() Ensure compliance with various regulatory requirements at all levels of government, align internal policies with laws and standards, and stay up-to-date with regulatory changes.
Ensure compliance with various regulatory requirements at all levels of government, align internal policies with laws and standards, and stay up-to-date with regulatory changes.![]() Real-time risk intelligence across your enterprise can help you mitigate IT and cyber risks proactively, ensure compliance with IT regulations and standards, and achieve a unified view of risks, threats, and vulnerabilities.
Real-time risk intelligence across your enterprise can help you mitigate IT and cyber risks proactively, ensure compliance with IT regulations and standards, and achieve a unified view of risks, threats, and vulnerabilities.![]() Manage third and fourth-party risks to safeguard your ecosystem. Identify, assess, and mitigate risks. Ensure compliance and track performance. Identify and assess business continuity risks. Use advanced reporting tools to manage risks proactively.
Manage third and fourth-party risks to safeguard your ecosystem. Identify, assess, and mitigate risks. Ensure compliance and track performance. Identify and assess business continuity risks. Use advanced reporting tools to manage risks proactively.![]() Optimize assurance processes by implementing agile risk-based audits, enabling agile internal audit processes, and streamlining SOX surveys and certifications. This will save time and reduce costs while establishing well-defined workflows and efficient risk assessment planning.
Optimize assurance processes by implementing agile risk-based audits, enabling agile internal audit processes, and streamlining SOX surveys and certifications. This will save time and reduce costs while establishing well-defined workflows and efficient risk assessment planning.![]() Ensure uninterrupted operations, recover faster from crises, and manage an effective business continuity and disaster recovery program with a flexible, integrated, and robust platform.
Ensure uninterrupted operations, recover faster from crises, and manage an effective business continuity and disaster recovery program with a flexible, integrated, and robust platform.![]() Take advantage of AI-assisted policy templates to streamline the process.
Take advantage of AI-assisted policy templates to streamline the process.

The impact of potential cyber attacks on the financial sectors has become business critical. Currently, over half of all financial companies had been affected by cyber attacks, and companies in the financial and insurance sector have been hit more often than average at around 60 percent. ISO certification is not enough. Both national organizations such as the Federal Office for Information Security (Bundesamt für Sicherheit in der Informationstechnik or BSI) and international organizations like the International Monetary Fund (IMF) view the increasing number of cyber attacks as a danger to financial stability.

ISO certification has not cured the rampant cyber crimes. Cybercrime has become the new normal and is greatly affecting the resource industry. Every day, crimes are committed against leading companies that were thought to have top security protocols in place. Cybercrime continues to cause a serious financial impact on economies. Issues such as stolen confidential business information, online fraud, financial manipulation and the cost of securing networks after hacking are some of the most devastating effects on companies that refuse to implement the right ISMS.

Healthcare centers are in a tight spot. As administrative technologies like electronic health records (EHRs) and patient and provider portals become standard issue in healthcare organizations, the access to data and information so strongly demanded by patients, providers, payers, and employees is also fast becoming a target of scrutiny and risk. Regulations such as the Health Insurance Portability and Accountability Act (HIPAA) require healthcare organizations to implement administrative, physical and technical safeguards to ensure the integrity and privacy of patient records and other sensitive medical data is not enough to fight against cybercrimes.

Cybersecurity, as it should be, is a concern for all organizations and the energy sector is no different. “Stuxnet, a malicious computer worm that targeted SCADA (supervisory control and data acquisition) systems in 2010, was a watershed moment for the sector,” explains Sloan. “It showed how a cyber attack can have a serious impact on the physical, as well as the digital, world.” However, while data breaches are prevalent, the subject of cyber security in the energy sector should be of perhaps greater concern using a comprehensive ISMS tool.

As government services go digital, criminals are spotting new opportunities for fraudulent claims and theft. Around the world, the digitization of government is gathering pace, with a host of interactions now carried out online. In some countries, you can vote, pay bills and taxes, and get medical prescriptions – often using a single, digital citizen ID that’s stored centrally.

Consumer trust is a vital issue in every organization. Cetbix ISMS empirically analyzes the key factors that influence the adoption of innovation in an organization. For example, the advancement of mobile devices and cloud adoption have increased the uptake of innovation. Technology security threats have increased tremendously and have become a challenge for both users and innovators. Cetbix empirically inspects the components that influence the expectations of both your users and organizations to adopt a secure methodology, such as customer trust and data security.
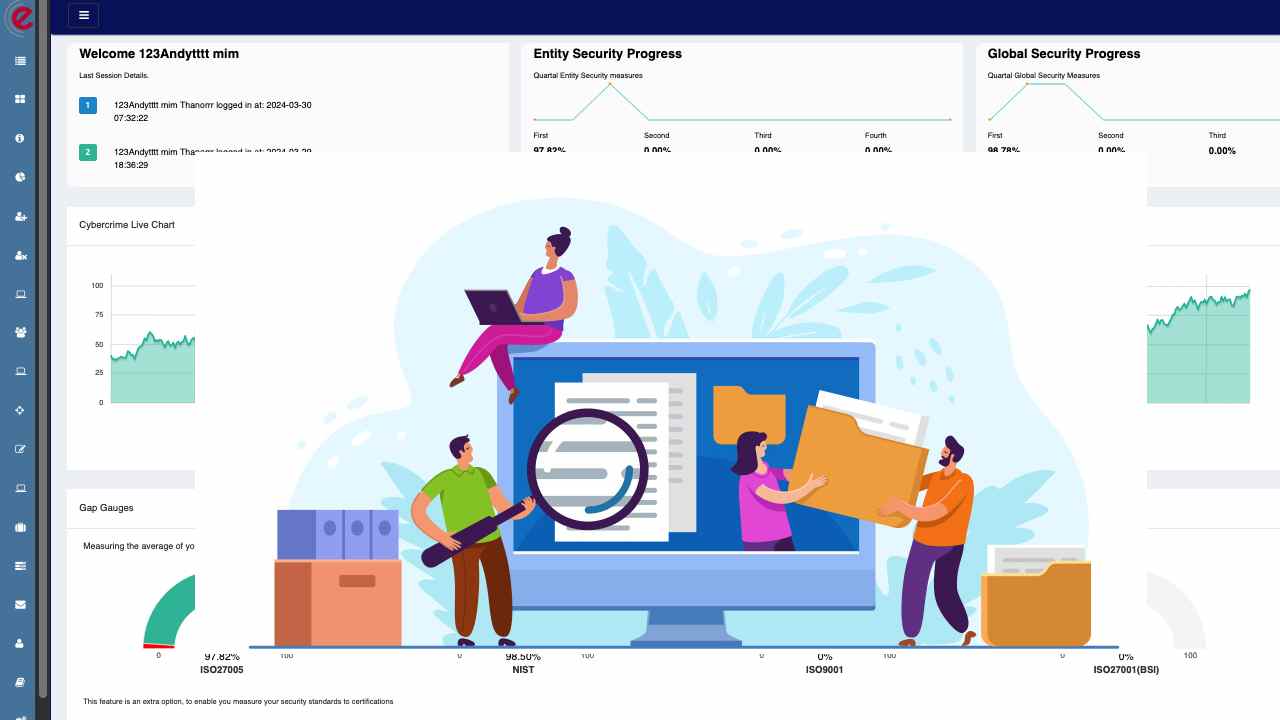
Switch to Cetbix for continuous control testing. With cross-mapping support and automated alerts, cetbix helps control owners take swift action when items fall out of compliance.

Simplify risk assessment with Cetbix. Customize your risk register and track your risk exposure over time with reporting.
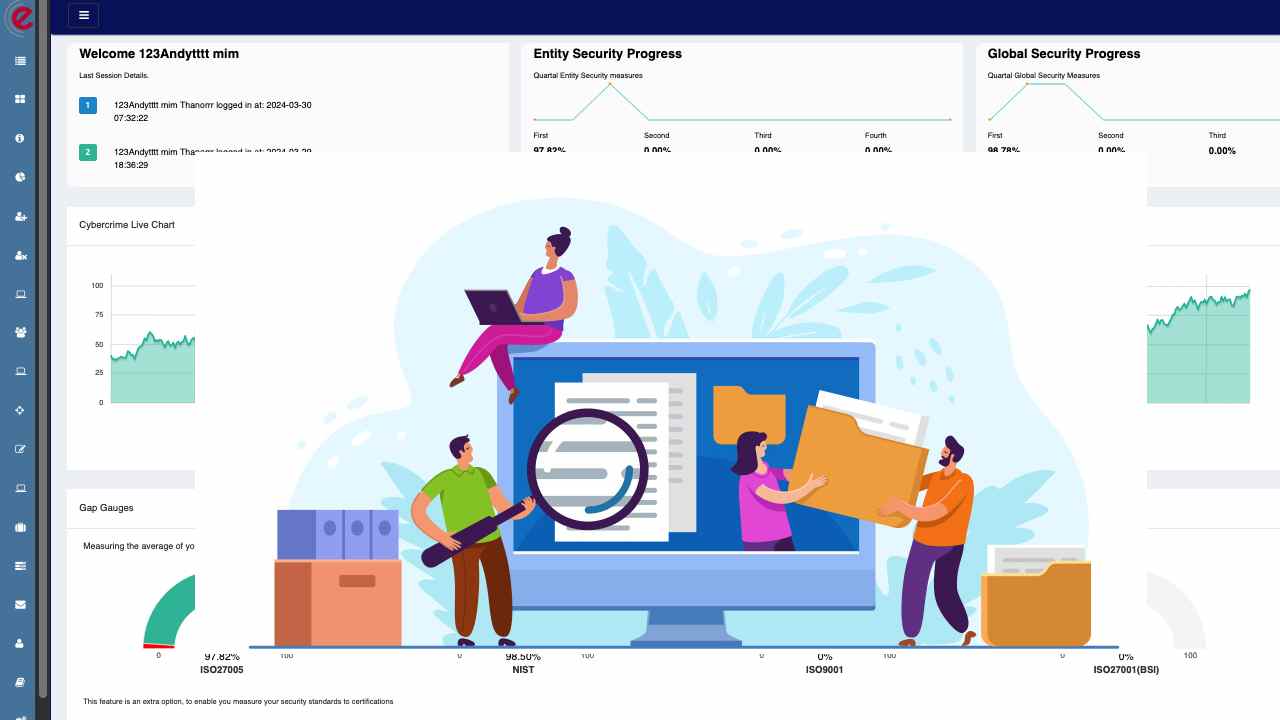
Data-driven solution for efficient and targeted implementation of IT-supported processes, including information security, data protection, and risk management.
Most ISMS tools focus on ISO27001 certification and neglect cybercrime prevention. Certification does not convey security. Furthermore, Artificial Intelligence (AI) in cybersecurity has also evolved from the FUD factor to buzzword. However, AI is neither a silver bullet for today cybercrime, human intelligence, and multi-cloud environments.
Information security development has a huge impact on the quality of information and the technical mechanisms used to protect information assets.
We provide a unified database that links your current standards, guidelines, and assessments, saving you valuable time and ensuring quality. This allows you to monitor and manage your organization's risks effectively. Cetbix GRC management platform offers transparency and security to your organization, making it a reliable and secure solution.