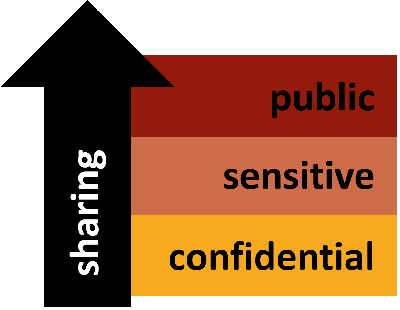
In the Cetbix data classification approach which is a combination of the cetbix data inventory, data is grouped and restricted according to the data classification scheme defined in Cetbix. This term is often used interchangeably with sensitive data. Cetbix data classification consists of "Internal Information" which is held at the information that is classified as Private or Restricted Information according to the data classification scheme defined in an organization policy. Cetbix Data classification, in the context of information security, classifies data based on the level of sensitivity and the impact to the organization should that data be disclosed, altered or destroyed without authorization. The classification of data helps determine what baseline security controls are appropriate for safeguarding that data. Cetbix classifies data into one of three sensitivity levels, or classifications: Internal (Restricted Data), External (Public Data) and Secure (Private Data).
In the concept of Cetbix data classification, sensitive data is defined and rules are established for its protection base on your organization policy.
Cetbix data classification neglects complex languages that make it difficult for CISO, CIO and Security Managers to understand and follow without any question. Due to its flexibility, it can fit into the organization’s workflows and outlines the responsibilities of all parties. As your organization grows and evolves and business needs change, Cetbix data classification policy can be simply adjusted to fit the changes.
Data classification policy
Cetbix takes your data classification policy document, analyses it and establishes a classification framework focusing on a list of responsibilities for identifying sensitive data and descriptions of the various data classification levels.
.png)
Requirements for protecting
Cetbix data classification policy separates requirements for how the data must be handled from the classification policy. Here, a separate document that defines the requirements for the protection of each class of information is automatically developed. Cetbix can also use specific information-handling documents if your organization has unique needs.
Confidential Data
Data strategies differ ( greatly from one organization to the next, as each generates different types and volumes of data. The balance may vary greatly from one user to the next between office documents, email correspondence, images, video files, customer and product information, financial data, and so on. Confidentiality is, however, important to all organizations.
Cetbix ISMS automatically enables CISO, CIO and security leaders to gather enough information from C-level and system leaders. With the help of the Cebit "intelligent-approach" CISOs are able to seek the support of someone from C-level or the executive board who understands the importance of classification and the risks associated with data. Further, you can use this help to work closely together with the business stakeholders on the next steps.
Cetbix ISMS defines the purpose of sensitive data classification. You need to articulate why you need a data classification policy. Depending on your organization’s structure, business processes, and other factors, your goal for creating data classification policy might be one or more of the following: To map data protection levels to the organization’s needs, budgets and resource constraints. To mitigate the risks associated with unauthorized disclosure and access. To comply with industry standards that require information classification (e.g., ISO 27001), retrieve specific information in a set timeframe (e.g., GDPR), or store information only in specific locations with limited access (e.g., PCI DSS).