Unlock Comprehensive Solutions with Cetbix
Empower your organization with Cetbix's AI-driven platform, designed to tackle critical security and compliance challenges through comprehensive solutions such as SaaS Governance, Risk & Compliance (GRC) Automation, Information Security Management System (ISMS), IT & OT Asset Management, Risk Assessment, Quality Management, Document Management, Third-Party Management, Digital Transformation Strategies, and seamless compliance with standards and frameworks like ISO, NIST, NIS2, SOC2, GDPR, ASCS Eight-Essentials, CIS, DORA, MiFID and more.
Transform your journey into a strategic advantage today!
Contact us for a demo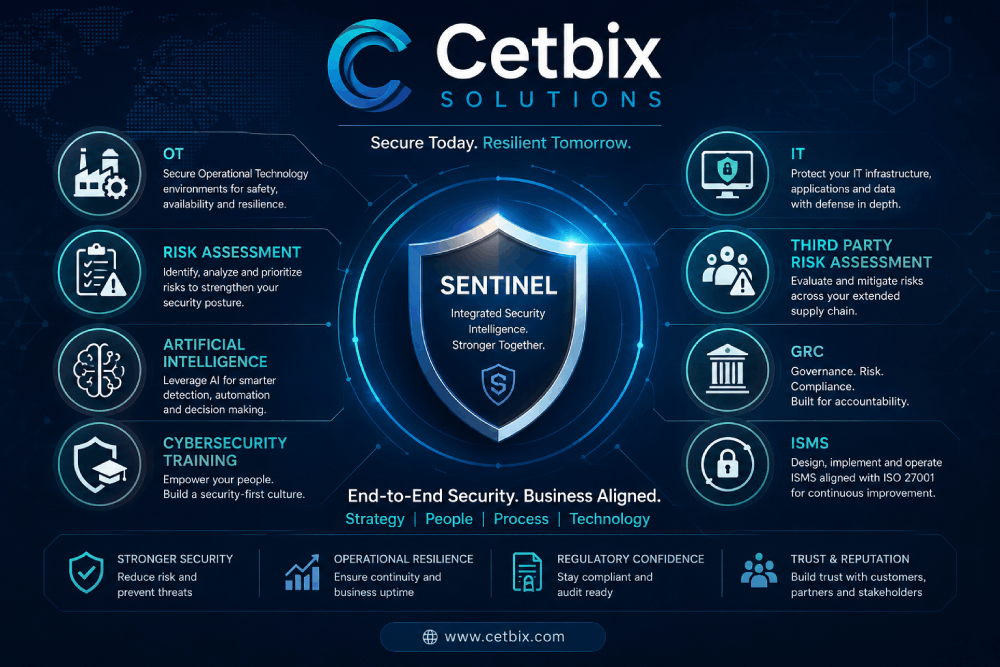
Trusted by Forward-Thinking Organizations Worldwide
Leading organizations across industries trust Cetbix to simplify compliance, strengthen cybersecurity, and drive operational excellence. From fast-growing startups to global enterprises, our clients rely on our AI-driven platform to manage risk, ensure regulatory compliance, and accelerate digital transformation with confidence.
Enterprise-Grade Security & Compliance
Comprehensive solutions tailored to meet the most rigorous industry standards and regulations
Cetbix: Empowering Organizations in Compliance, Risk, Governance and Cybersecurity
Cetbix is committed to empowering organizations to tackle their most critical security and compliance challenges head-on. With our innovative solutions, you can transform your compliance journey into a strategic advantage while enhancing your overall cybersecurity posture.
Key Solutions Offered By Cetbix
In today’s complex digital landscape, organizations face a myriad of challenges related to compliance and cybersecurity. Cetbix offers a comprehensive suite of AI-driven solutions designed to help businesses navigate these challenges effectively. Our platform not only addresses compliance requirements but also enhances overall security and operational efficiency.
Governance, Risk, and Compliance (GRC) Automation
Streamline your compliance processes across multiple frameworks, including ISO 27001, NIST, SOC2, TISAX®, NIS2, and IATF 16949. Our GRC automation tools help you maintain adherence to regulatory standards while minimizing manual efforts.
AI-Driven Information Security Management System (ISMS)
Implement robust information security practices with our AI-driven ISMS. This solution enables organizations to monitor their security posture continuously, ensuring that all critical assets are protected against emerging threats.
Enterprise Risk Management (ISO 31000 / COSO ERM)
ISO 31000 and COSO ERM are standards that provide guidelines for risk management applicable to organizations of any type and size. Their primary goal is to help organizations systematically identify, assess, manage, and monitor risks to create and protect value.
Asset Management
Manage your assets effectively by identifying, tracking, and securing all hardware and software components within your organisation. Our asset management solutions ensure business continuity and protect against cyber threats.
Operational Technology (IEC 62443, ISO27019)
Manage your OT effectively by identifying, tracking, and securing all hardware and software components within your operational environment. Cetbix OT solutions ensure operational continuity and protect against cyber threats.
Risk Assessment Tools
Conduct thorough risk assessments for both IT and OT environments. Our tools help identify vulnerabilities, assess potential impacts, and prioritize risks for effective mitigation strategies.
Facilitates Digital Transformation
Implementing the EU Whistleblowing Directive not only fosters a culture of transparency and integrity within organizations but also mitigates risks associated with non-compliance. By encouraging reporting of unethical practices, organizations can address issues proactively, enhancing their reputation and operational resilience.
QMS/EHS: Integrated Compliance for ISO 14001 & 45001
Cetbix tackles environmental, health, and safety (EHS) through its flexible Quality Management System (QMS), supporting ISO 14001 (Environmental Management) and ISO 45001 (Occupational Health & Safety). Both standards leverage the High-Level Structure (HLS) with PDCA cycles, risk-based thinking, leadership commitment, and performance evaluation, enabling seamless integration into a unified EHS system managed via Cetbix.
Document Management System
Streamline document control processes to enhance compliance efforts. Our system ensures that all documentation is up-to-date, accessible, and aligned with industry standards.
Third-Party Risk Management
Assess and manage risks associated with external vendors effectively. Our third-party management tools help ensure that your supply chain remains secure and compliant with regulations.
Vendor Risk Management
Manage vendor relationships with confidence by documenting vendor risk assessments and ensuring compliance with regulatory requirements. This comprehensive approach helps mitigate risks associated with third-party vendors.
Over 90% faster with AI and Automations
AI-driven solutions automate labor-intensive tasks such as risk assessments, compliance monitoring, and audit processes. This reduces the need for extensive manual intervention, allowing compliance teams to focus on strategic decision-making rather than routine tasks. For instance, automated evidence collection and reporting streamline audit workflows, saving time and resources while increasing accuracy.
EU Whistleblowing Directive with ease
Implementing the EU Whistleblowing Directive not only fosters a culture of transparency and integrity within organizations but also mitigates risks associated with non-compliance. By encouraging reporting of unethical practices, organizations can address issues proactively, enhancing their reputation and operational resilience.
Trust Center
Cetbix Trust Center is a centralized platform that strengthens transparency, security, and compliance across relationships with customers, suppliers, and partners. It offers a secure space to share cybersecurity, privacy, compliance, and risk management information, including certifications, policies, audit reports, vendor assessments, and due-diligence documents. By streamlining third-party risk management, supporting regulatory compliance, and providing ongoing security assurance and governance visibility, the Trust Center helps organizations build and maintain trust.
Sentinel Agentless Network Discovery (OT/IT) / License Management
Cetbix Sentinel Agentless Network Discovery (OT/IT) & License Management provides centralized visibility and control across OT and IT environments. It automatically discovers and classifies connected assets without agents, supporting continuous monitoring, asset inventory, vulnerability identification, and network visibility. The integrated License Management capability helps organizations manage licenses, subscriptions, contracts, renewals, and vendor agreements in one platform. Together, these capabilities improve cybersecurity, strengthen compliance, reduce risk, and optimize software usage across the organization.
Transform Your Compliance Journey
Into a Strategic Advantage
Contact us for a demo or more information on how Cetbix can help your organization navigate the complexities of compliance and cybersecurity effectively!

Hybrid Governance, Risk & Compliance - Cyber Security
Discover our most powerful solutions designed to streamline your compliance journey
Support for 35+ leading compliance frameworks—across information security, data privacy, AI governance, and more
Organization Strategic Transformation
Cetbix details the information that need to be addressed.
GRC, ISMS, TISAX & IATF
Document Management
Vendor Management & Risk Assessments
Asset Management
Application Management
Fleet Management System
Looking for expert advice on data security, privacy, and other compliance?
Our team of certified security experts is ready to help you navigate the complex landscape of data protection, privacy regulations, and compliance requirements.
Talk to expertWindows Manager Professional (WMP 2.7)
What Our Clients Say
Trusted by industry leaders worldwide